- Anti Run 2 4 Serial Key Download
- Anti Run 2 4 Serial Key Code
- Anti Run 2 4 Serial Key Free
- Antirun 2.4 Serial Key
OpenLDAP clients and servers are capable of using the
Bioshock 1.1.1 No Dvd Crack Mac Os X DOWNLOAD h a w x 2 pc incl crack The king of fighters 2010 movie Nokia c1 01 Queen - best of. For e65 mobile Advanced system optimizer 3 1 648 8773 key patch 10 5 leopard for. New version Keygen serial para antirun 2 4 No sex please were british. Com Teendreams models pavlina Ace dvd audio extractor 1.1.1 Flo rida low flp.
For generating certifcates, please reference http://www.openldap.org/faq/data/cache/185.html- Click to download: Download erdas imagine 2014 crack Download songs computer memory card crack download. Magic dvd copier 4.8 5 crack, atimetool 1.8 5 Cracked debDarwing Lopez Diaz alguien tiene el crack erdas 2015See Translation.
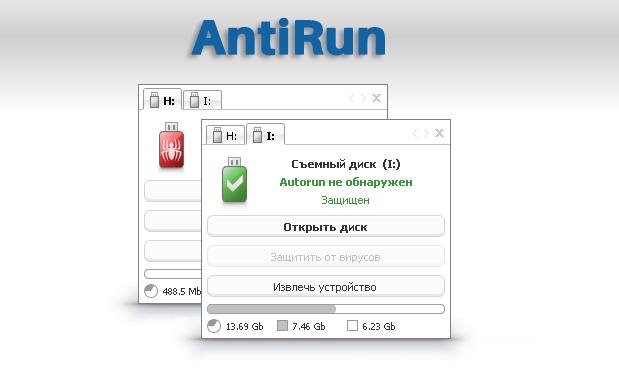
- Dwf2dwg Pro Serial Activation Key Visio 2003 Connector Dasar Dasar Jurnalistik Pdf Merge And Split Split Ply Braiding Tools. AntiRun 2.4 Pro Final.
- Serial numbers for these versions are emailed to you after you place an order or can be found in Autodesk Account. If you have physical media (a DVD or USB key) for a 2013 or earlier product, your serial number and product key will be printed on the label of the product packaging. Example of label from 2011 version.
- The serial number for AutoRun is available. This release was created for you, eager to use AutoRun 2.4 full and without limitations. Our intentions are not to harm AutoRun software company but to give the possibility to those who can not pay for any piece of software out there. This should be your intention too, as a user, to fully evaluate.
16.1. TLS Certificates
TLS uses
16.1.1. Server Certificates
The
16.1.2. Client Certificates
The DN of a client certificate can be used directly as an authentication DN. Since X.509 is a part of the
16.2. TLS Configuration
After obtaining the required certificates, a number of options must be configured on both the client and the server to enable TLS and make use of the certificates. At a minimum, the clients must be configured with the name of the file containing all of the
Typically a single CA will have issued the server certificate and all of the trusted client certificates, so the server only needs to trust that one signing CA. However, a client may wish to connect to a variety of secure servers managed by different organizations, with server certificates generated by many different CAs. As such, a client is likely to need a list of many different trusted CAs in its configuration.
16.2.1. Server Configuration
The configuration directives for slapd belong in the global directives section of slapd.conf(5).
'>16.2.1.1. TLSCACertificateFile <filename>
This directive specifies the
'>16.2.1.2. TLSCACertificatePath <path>
This directive specifies the path of a directory that contains individual
When using Mozilla NSS, this directive can be used to specify the path of the directory containing the NSS certificate and key database files. The certutil command can be used to add a
- This command will add a CA certficate stored in the PEM (ASCII) formatted
file named /path/to/cacertfile.pem. -t CT, means that the certificate is
trusted to be a CA issuing certs for use in TLS clients and servers.
'>16.2.1.3. TLSCertificateFile <filename>

This directive specifies the file that contains the slapd server certificate. Certificates are generally public information and require no special protection.
When using Mozilla NSS, if using a cert/key database (specified with TLSCACertificatePath), this directive specifies the name of the certificate to use:
- If using a token other than the internal built in token, specify the
token name first, followed by a colon:
- Use certutil -L to list the certificates by name:
'>16.2.1.4. TLSCertificateKeyFile <filename>
This directive specifies the file that contains the private key that matches the certificate stored in the TLSCertificateFile file. Private keys themselves are sensitive data and are usually password encrypted for protection. However, the current implementation doesn't support encrypted keys so the key must not be encrypted and the file itself must be protected carefully.
When using Mozilla NSS, this directive specifies the name of a file that contains the password for the key for the certificate specified with TLSCertificateFile. The modutil command can be used to turn off password protection for the cert/key database. For example, if TLSCACertificatePath specifes /etc/openldap/certdb as the location of the cert/key database, use modutil to change the password to the empty string:
- You must have the old password, if any. Ignore the WARNING about the running
browser. Press 'Enter' for the new password.
'>16.2.1.5. TLSCipherSuite <cipher-suite-spec>
This directive configures what ciphers will be accepted and the preference order. <cipher-suite-spec> should be a cipher specification for OpenSSL. You can use the command
to obtain a verbose list of available cipher specifications.
Besides the individual cipher names, the specifiers HIGH, MEDIUM, LOW, EXPORT, and EXPORT40 may be helpful, along with TLSv1, SSLv3, and SSLv2.
To obtain the list of ciphers in GnuTLS use:

When using Mozilla NSS, the OpenSSL cipher suite specifications are used and translated into the format used internally by Mozilla NSS. There isn't an easy way to list the cipher suites from the command line. The authoritative list is in the source code for Mozilla NSS in the file sslinfo.c in the structure
'>16.2.1.6. TLSRandFile <filename>
This directive specifies the file to obtain random bits from when /dev/urandom is not available. If the system provides /dev/urandom then this option is not needed, otherwise a source of random data must be configured. Some systems (e.g. Linux) provide /dev/urandom by default, while others (e.g. Solaris) require the installation of a patch to provide it, and others may not support it at all. In the latter case, EGD or PRNGD should be installed, and this directive should specify the name of the EGD/PRNGD socket. The environment variable RANDFILE can also be used to specify the filename. Also, in the absence of these options, the .rnd file in the slapd user's home directory may be used if it exists. To use the .rnd file, just create the file and copy a few hundred bytes of arbitrary data into the file. The file is only used to provide a seed for the pseudo-random number generator, and it doesn't need very much data to work.
This directive is ignored with GnuTLS and Mozilla NSS.
'>16.2.1.7. TLSDHParamFile <filename>
This directive specifies the file that contains parameters for Diffie-Hellman ephemeral key exchange. This is required in order to use DHE-based cipher suites, including all DSA-based suites (i.e. TLSCertificateKeyFile points to a DSA key), and RSA when the 'key encipherment' key usage is not specified in the certificate. Parameters can be generated using the following command
This directive is ignored with Mozilla NSS.
'>16.2.1.8. TLSECName <name>
This directive specifies the curve to use for Elliptic Curve Diffie-Hellman ephemeral key exchange. This is required in order to use ECDHE-based cipher suites in OpenSSL. The names of supported curves may be shown using the following command
This directive is not used for GnuTLS and is ignored with Mozilla NSS. For GnuTLS the curves may be specified in the ciphersuite.
16.2.1.9. TLSVerifyClient { never | allow | try | demand }
This directive specifies what checks to perform on client certificates in an incoming TLS session, if any. This option is set to never by default, in which case the server never asks the client for a certificate. With a setting of allow the server will ask for a client certificate; if none is provided the session proceeds normally. If a certificate is provided but the server is unable to verify it, the certificate is ignored and the session proceeds normally, as if no certificate had been provided. With a setting of try the certificate is requested, and if none is provided, the session proceeds normally. If a certificate is provided and it cannot be verified, the session is immediately terminated. With a setting of demand the certificate is requested and a valid certificate must be provided, otherwise the session is immediately terminated.
Note: The server must request a client certificate in order to use the SASL EXTERNAL authentication mechanism with a TLS session. As such, a non-default TLSVerifyClient setting must be configured before SASL EXTERNAL authentication may be attempted, and the SASL EXTERNAL mechanism will only be offered to the client if a valid client certificate was received.16.2.2. Client Configuration
Most of the client configuration directives parallel the server directives. The names of the directives are different, and they go into ldap.conf(5) instead of slapd.conf(5), but their functionality is mostly the same. Also, while most of these options may be configured on a system-wide basis, they may all be overridden by individual users in their .ldaprc files.
The LDAP Start TLS operation is used in LDAP to initiate TLS negotiation. All OpenLDAP command line tools support a -Z and -ZZ flag to indicate whether a Start TLS operation is to be issued. The latter flag indicates that the tool is to cease processing if TLS cannot be started while the former allows the command to continue.
In LDAPv2 environments, TLS is normally started using the LDAP Secure URI scheme (ldaps://) instead of the normal LDAP URI scheme (ldap://). OpenLDAP command line tools allow either scheme to used with the -H flag and with the URIldap.conf(5) option.
'>16.2.2.1. TLS_CACERT <filename>
This is equivalent to the server's TLSCACertificateFile option. As noted in the TLS Configuration section, a client typically may need to know about more CAs than a server, but otherwise the same considerations apply.
'>16.2.2.2. TLS_CACERTDIR <path>
Anti Run 2 4 Serial Key Download
This is equivalent to the server's TLSCACertificatePath option. The specified directory must be managed with the OpenSSL c_rehash utility as well. If using Mozilla NSS, <path> may contain a cert/key database.
'>16.2.2.3. TLS_CERT <filename>
This directive specifies the file that contains the client certificate. This is a user-only directive and can only be specified in a user's .ldaprc file.
When using Mozilla NSS, if using a cert/key database (specified with TLS_CACERTDIR), this directive specifies the name of the certificate to use:
- If using a token other than the internal built in token, specify the
token name first, followed by a colon:
- Use certutil -L to list the certificates by name:
'>16.2.2.4. TLS_KEY <filename>
This directive specifies the file that contains the private key that matches the certificate stored in the TLS_CERT file. The same constraints mentioned for TLSCertificateKeyFile apply here. This is also a user-only directive.
'>16.2.2.5. TLS_RANDFILE <filename>
Anti Run 2 4 Serial Key Code
This directive is the same as the server's TLSRandFile option.
Anti Run 2 4 Serial Key Free
16.2.2.6. TLS_REQCERT { never | allow | try | demand }
Antirun 2.4 Serial Key
This directive is equivalent to the server's TLSVerifyClient option. However, for clients the default value is demand and there generally is no good reason to change this setting.